This a guide on how to setup Wireguard VPN on Ubuntu and setting up a Wireguard client.
Requirements:
1. Ubuntu Server 20.04 used in my lab. (20.04 or higher is required for Policy routing)
2. Ubuntu Client (Ubuntu 20.04)
3. Root access to the server.
4. Network Access
Note: This should also work on Linux Mint 20.04
Setting up the Wireguard Server
Login to the In my lab, I have set up a EC2 instance and below is the current IP configuration before setting up Wireguard.
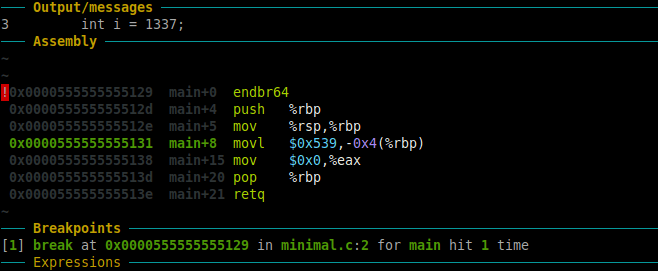
root@ip-172-31-20-229:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 9001 qdisc fq_codel state UP group default qlen 1000
link/ether 02:ca:92:5f:0e:80 brd ff:ff:ff:ff:ff:ff
inet 172.31.20.229/20 brd 172.31.31.255 scope global dynamic eth0
valid_lft 2617sec preferred_lft 2617sec
inet6 fe80::ca:92ff:fe5f:e80/64 scope link
valid_lft forever preferred_lft forever
From above, I have a single interface with IP 172.31.20.229 assigned to eth0.
sudo apt update && sudo apt upgrade -y sudo apt install wireguard -y
-Switch to root and run the following:
sudo su –
Below are the default permissions on the wireguard dir:
root@ip-172-31-20-229:~# ls -l /etc/ | grep wireguard drwx------ 2 root root 4096 Aug 4 2020 wireguard
-You could set permissions to the directory as follows:
chmod 0700 /etc/wireguard/ root@ip-172-31-20-229:~# ls -l /etc/ | grep wireguard drwx------ 2 root root 4096 Aug 4 2020 wireguard
To check the version of Wireguard installed:
root@ip-172-31-20-229:/etc/wireguard# wg --version wireguard-tools v1.0.20200513 - https://git.zx2c4.com/wireguard-tools/
-Generate public and private key pairs:
cd /etc/wireguard/ umask 077; wg genkey | tee privatekey | wg pubkey > publickey
This should generate the private and the public key:
root@ip-172-31-20-229:/etc/wireguard# ls -l total 8 -rw------- 1 root root 45 Jun 30 20:23 privatekey -rw------- 1 root root 45 Jun 30 20:23 publickey
-Take a note of the private key “privatekey” cat privatekey . You will need to add this to the WG server’s conf file.
Setting up the Wireguard Server’s configuration file
vim /etc/wireguard/wg0.conf
Add below content. (Here, I chose the IP as 192.168.6.1 which is the new VPN private address that will be assigned to the interface)
[Interface] ## My VPN server private IP address ## Address = 192.168.6.1 ## My VPN server port ## ListenPort = 41194 ## VPN server's private key i.e. string from /etc/wireguard/privatekey ## PrivateKey = ADD_PRIVATE_KEY_HERE
-Allow the port in the Server’s Firewall:
root@ip-172-31-20-229:~# sudo ufw allow 41194/udp Rules updated Rules updated (v6)
-To check the status:
sudo ufw status
– Enable wireguard service on boot on the server and start the service:
ubuntu@ip-172-31-20-229:~$ sudo systemctl enable wg-quick@wg0 Created symlink /etc/systemd/system/multi-user.target.wants/[email protected] → /lib/systemd/system/[email protected]. ubuntu@ip-172-31-20-229:~$ sudo systemctl start wg-quick@wg0
To check the status of the wireguard service, use the following:
root@ip-172-31-20-229:~# sudo systemctl status wg-quick@wg0 ● [email protected] - WireGuard via wg-quick(8) for wg0 Loaded: loaded (/lib/systemd/system/[email protected]; enabled; vendor preset: enabled) Active: active (exited) since Thu 2022-06-30 21:29:01 UTC; 8min ago Docs: man:wg-quick(8) man:wg(8) https://www.wireguard.com/ https://www.wireguard.com/quickstart/ https://git.zx2c4.com/wireguard-tools/about/src/man/wg-quick.8 https://git.zx2c4.com/wireguard-tools/about/src/man/wg.8 Process: 2230 ExecStart=/usr/bin/wg-quick up wg0 (code=exited, status=0/SUCCESS) Main PID: 2230 (code=exited, status=0/SUCCESS) Jun 30 21:29:01 ip-172-31-20-229 systemd[1]: [email protected]: Succeeded. Jun 30 21:29:01 ip-172-31-20-229 systemd[1]: Stopped WireGuard via wg-quick(8) for wg0. Jun 30 21:29:01 ip-172-31-20-229 systemd[1]: Starting WireGuard via wg-quick(8) for wg0... Jun 30 21:29:01 ip-172-31-20-229 wg-quick[2230]: [#] ip link add wg0 type wireguard Jun 30 21:29:01 ip-172-31-20-229 wg-quick[2230]: [#] wg setconf wg0 /dev/fd/63 Jun 30 21:29:01 ip-172-31-20-229 wg-quick[2230]: [#] ip -4 address add 192.168.6.1/24 dev wg0 Jun 30 21:29:01 ip-172-31-20-229 wg-quick[2230]: [#] ip link set mtu 8921 up dev wg0 Jun 30 21:29:01 ip-172-31-20-229 systemd[1]: Finished WireGuard via wg-quick(8) for wg0.
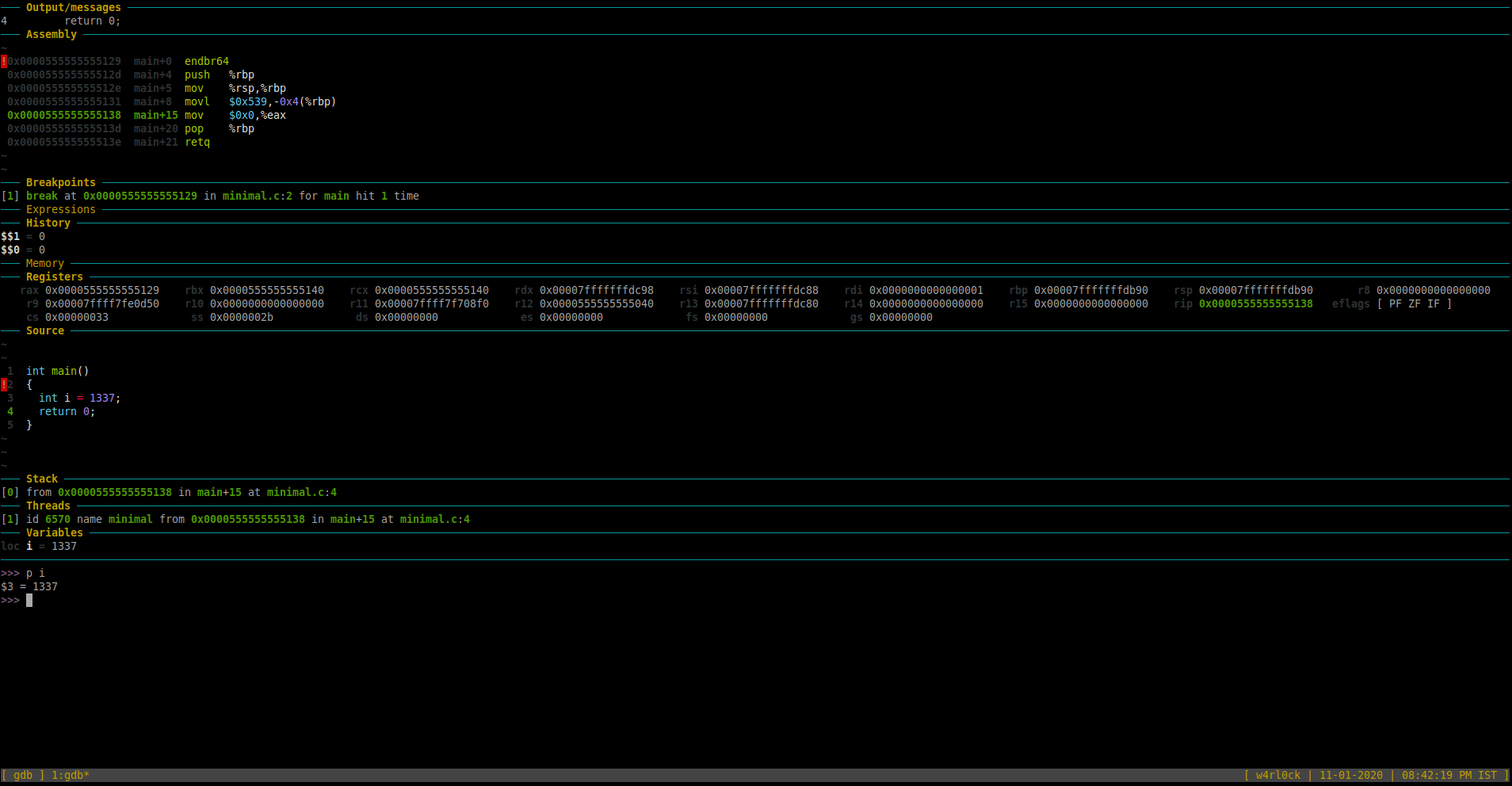
Checking the ifconfig output, you would see a new interface wg0 is created automatically which is expected.
root@ip-172-31-20-229:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 9001 qdisc fq_codel state UP group default qlen 1000
link/ether 02:ca:92:5f:0e:80 brd ff:ff:ff:ff:ff:ff
inet 172.31.20.229/20 brd 172.31.31.255 scope global dynamic eth0
valid_lft 2235sec preferred_lft 2235sec
inet6 fe80::ca:92ff:fe5f:e80/64 scope link
valid_lft forever preferred_lft forever
5: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 8921 qdisc noqueue state UNKNOWN group default qlen 1000
link/none
inet 192.168.6.1/24 scope global wg0
valid_lft forever preferred_lft forever
– You can check wireguard information/stats using the below command:
ubuntu@ip-172-31-20-229:~$ sudo wg interface: wg0 public key: pHrkGojLiNZy2GwshmdEXMaaOmowXXXXXXXXXXXXXXX= private key: (hidden) listening port: 41194
Configuring the VPN Client
- Login to the client and install Wireguard.
sudo apt install wireguard -y
– Create the configuration file
root@wg-client:~# sudo sh -c 'umask 077; touch /etc/wireguard/wg0.conf' root@wg-client:~# ls -l /etc/wireguard/wg0.conf -rw------- 1 root root 0 Jun 30 20:58 /etc/wireguard/wg0.conf
- Create a key pair in the client
– In the client machine, create a key pair:
root@wg-client:~# cd /etc/wireguard/ root@wg-client:/etc/wireguard# umask 077; wg genkey | tee privatekey | wg pubkey > publickey root@wg-client:/etc/wireguard# ls -l total 8 -rw------- 1 root root 45 Jun 30 21:01 privatekey -rw------- 1 root root 45 Jun 30 21:01 publickey -rw------- 1 root root 0 Jun 30 20:58 wg0.conf root@wg-client:/etc/wireguard#
– Take a note of the client’s public key. (This will be added in the server’s config later)
-Take a note of the private key from the client. This will be added in its own config file.
cat privatekey
– On the client, create the wireguard config file as below:
[Interface] ## Add the client's private key which is from /etc/wireguard/publickey ## PrivateKey = CLIENT_PRIVATE_KEY_HERE ## Client ip address that will be set by this Client ## Address = 192.168.6.2/24 [Peer] ## Ubuntu 20.04 server public key ## PublicKey = SERVER_PUBLIC_KEY_HERE ## set ACL ## AllowedIPs = 192.168.2.0/24 ## Your Ubuntu 20.04 LTS server's public IPv4/IPv6 address and port ## Endpoint = PUBLIC_IP_OF_YOUR_WIREGUARD_SERVER:41194 ## Key connection alive ## PersistentKeepalive = 15
-On the client, enable and start the Wireguard service:
root@wg-client:/etc/wireguard# sudo systemctl enable wg-quick@wg0 Created symlink /etc/systemd/system/multi-user.target.wants/[email protected] -> /lib/systemd/system/[email protected]. root@wg-client:/etc/wireguard# sudo systemctl start wg-quick@wg0
– Check the status of the service in the client:
root@wg-client:~# sudo systemctl status wg-quick@wg0 * [email protected] - WireGuard via wg-quick(8) for wg0 Loaded: loaded (/lib/systemd/system/[email protected]; enabled; vendor preset: enabled) Active: active (exited) since Thu 2022-06-30 21:35:17 UTC; 5min ago Docs: man:wg-quick(8) man:wg(8) https://www.wireguard.com/ https://www.wireguard.com/quickstart/ https://git.zx2c4.com/wireguard-tools/about/src/man/wg-quick.8 https://git.zx2c4.com/wireguard-tools/about/src/man/wg.8 Process: 123 ExecStart=/usr/bin/wg-quick up wg0 (code=exited, status=0/SUCCESS) Main PID: 123 (code=exited, status=0/SUCCESS) CPU: 28ms Jun 30 21:35:17 wg-client systemd[1]: Starting WireGuard via wg-quick(8) for wg0... Jun 30 21:35:17 wg-client wg-quick[123]: [#] ip link add wg0 type wireguard Jun 30 21:35:17 wg-client wg-quick[123]: [#] wg setconf wg0 /dev/fd/63 Jun 30 21:35:17 wg-client wg-quick[123]: [#] ip -4 address add 192.168.6.2/24 dev wg0 Jun 30 21:35:17 wg-client wg-quick[123]: [#] ip link set mtu 1420 up dev wg0 Jun 30 21:35:17 wg-client systemd[1]: Finished WireGuard via wg-quick(8) for wg0.
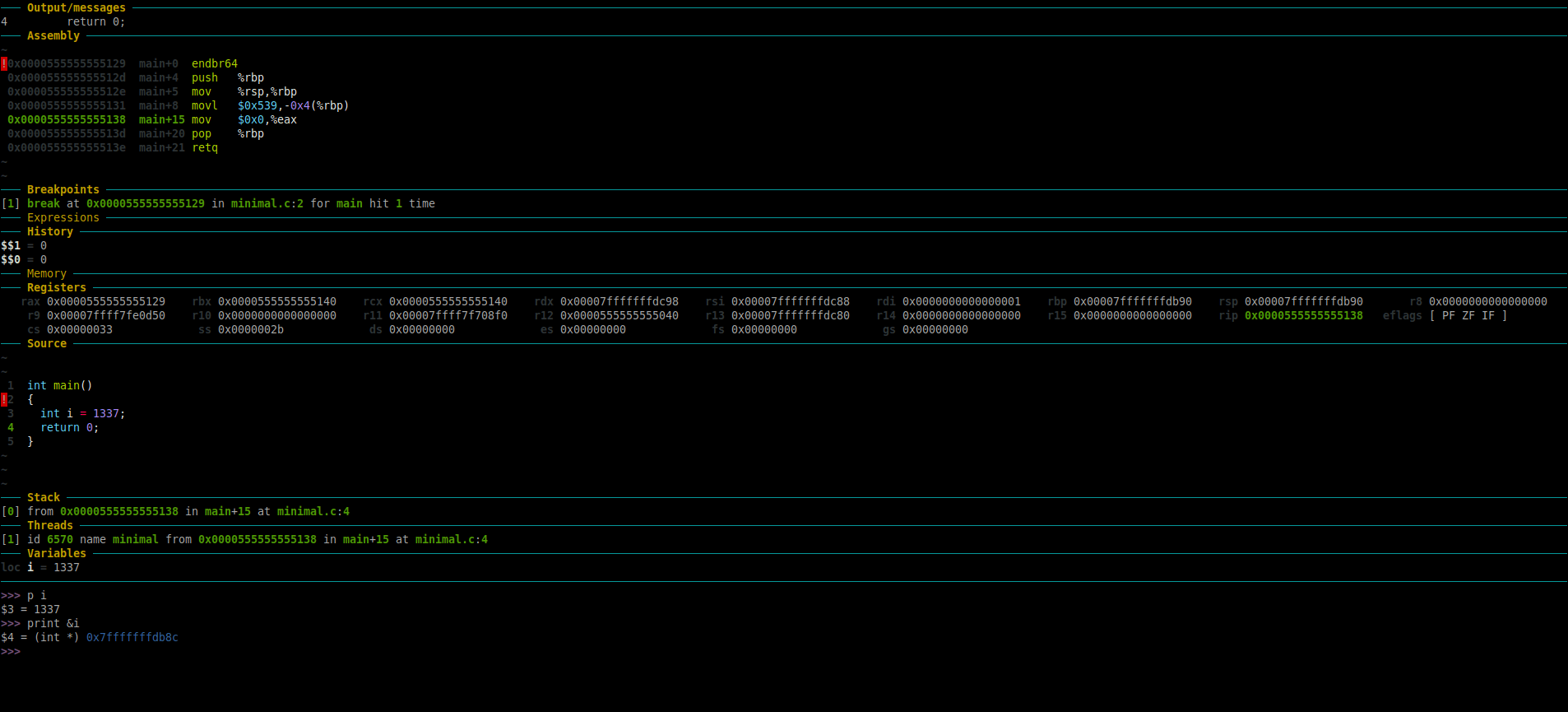
-From the above output, we can see that the wireguard service has created the interface wg0 and assigned the IP 192.168.6.2/24 to it. You could also verify this by checking by checking the device ip conf as below:
root@wg-client:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0@if114: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether aa:3c:37:57:21:8a brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.1.143/24 brd 192.168.1.255 scope global dynamic eth0
valid_lft 86010sec preferred_lft 86010sec
inet6 fe80::a83c:37ff:fe57:218a/64 scope link
valid_lft forever preferred_lft forever
3: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000
link/none
inet 192.168.6.2/24 scope global wg0
valid_lft forever preferred_lft forever
So far, we can configured the client to talk to the server. But the Server does not know about the client. So, next we need to update the Server’s Wireguard configuration file with the details of the wireguard client.
-Login to the Wireguard Server and add the below block to the server’s wireguard conf:
[Peer] ## Desktop/client VPN public key ## PublicKey = CLIENT_PUB_KEY_HERE ## client VPN IP address (note the /32 subnet) ## AllowedIPs = 192.168.6.2/32
-So, your Wireguard server’s configuration file will be as follows:
[Interface] ## My VPN server private IP address ## Address = 192.168.6.1 ## My VPN server port ## ListenPort = 41194 ## VPN server's private key i.e. /etc/wireguard/privatekey ## PrivateKey = ADD_PRIVATE_KEY_HERE [Peer] ## Desktop/client VPN public key ## PublicKey = CLIENT_PUB_KEY_HERE ## client VPN IP address (note the /32 subnet) ## AllowedIPs = 192.168.6.2/32
– Start the service again on the server:
sudo systemctl start wg-quick@wg0
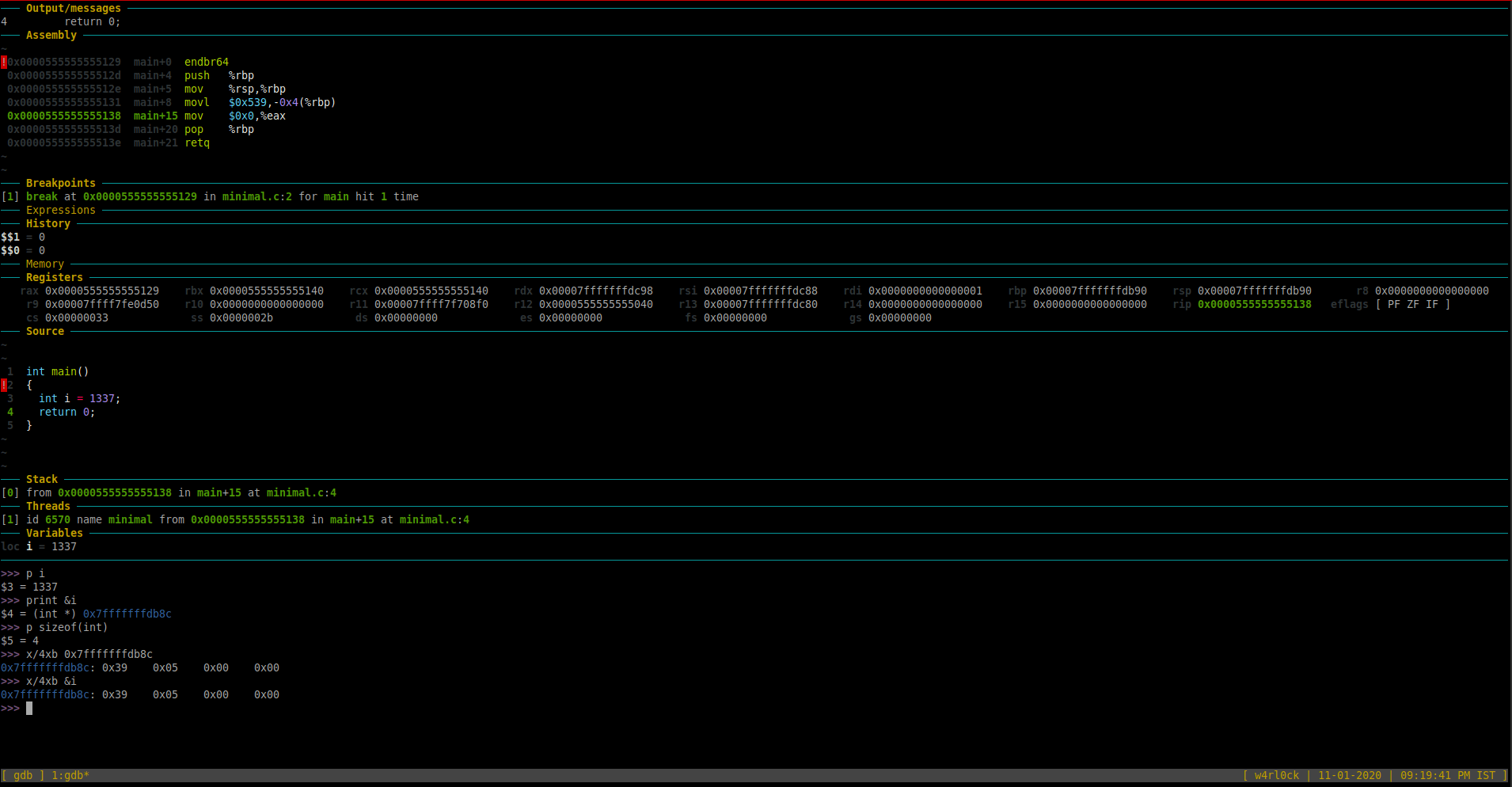
Verify connectivity from the client => server:
– If the server is in the cloud, then update the security groups tallow the port.
– From the client, ping the server 192.168.6.1
root@wg-client:~# ping 192.168.6.1 PING 192.168.6.1 (192.168.6.1) 56(84) bytes of data. 64 bytes from 192.168.6.1: icmp_seq=1 ttl=64 time=81.9 ms 64 bytes from 192.168.6.1: icmp_seq=2 ttl=64 time=82.5 ms ^C --- 192.168.6.1 ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1001ms rtt min/avg/max/mdev = 81.886/82.172/82.458/0.286 ms
Checking active connections from Wireguard server:
– To see which clients are connected to the server and the statistics, you can run the below:
root@ip-172-31-20-229:~# sudo wg interface: wg0 public key: pHrkGojLiNZy2GwshmdEXMaaOmowXXXXXXXXXXXXXXX= private key: (hidden) listening port: 41194 peer: 8Zp7Cji5Aseew3L0P3c35sUzJNIPYYYYYYYYYYYYYYY= endpoint: 1.2.3.4:33395 allowed ips: 192.168.6.2/32 latest handshake: 1 minute, 12 seconds ago transfer: 3.94 KiB received, 1.47 KiB sent
Additional Information:
For debugging issue with wireguard, you could check the logs:
sudo journalctl -eu wg-quick@wg0
Here is a little cronjob to monitor the tunnel via ping and restart tunnel: (Credits to linuxbabe)
sudo crontab -e
-Add the below:
SHELL=/bin/bash * * * * * for ((i=1; i<=6; i++)) do (ping -c9 192.168.6.1 > /dev/null || systemctl restart wg-quick@wg0) done
Hope this helps! Cheers!
Sources/References:
https://www.cyberciti.biz/faq/ubuntu-20-04-set-up-wireguard-vpn-server/
Set Up Your Own WireGuard VPN Server on Ubuntu 24.04/22.04/20.04



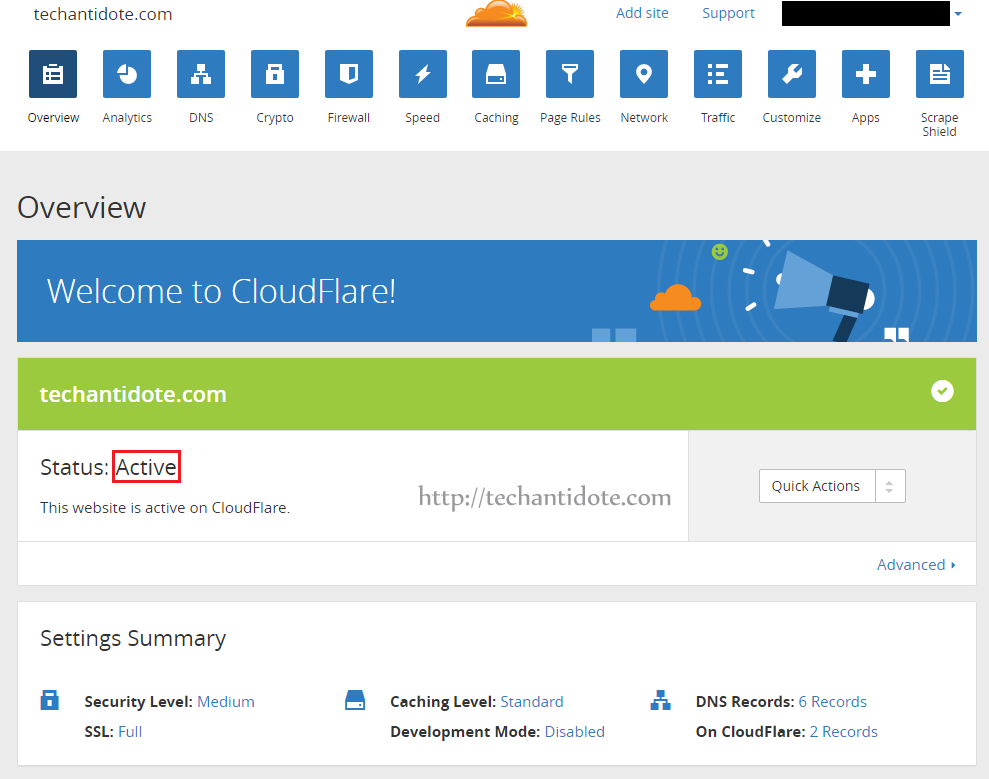 [NOTE: If you the status does not show as “Active” then you can click on “Recheck Status” and it then should show that its “Active”]
[NOTE: If you the status does not show as “Active” then you can click on “Recheck Status” and it then should show that its “Active”]